Ever felt underprepared for that crucial job interview? Or perhaps you’ve landed the interview but struggled to articulate your skills and experiences effectively? Fear not! We’ve got you covered. In this blog post, we’re diving deep into the Certified Information Systems Security Professional (CISSP) interview questions that you’re most likely to encounter. But that’s not all. We’ll also provide expert insights into the key responsibilities of a Certified Information Systems Security Professional (CISSP) so you can tailor your answers to impress potential employers.
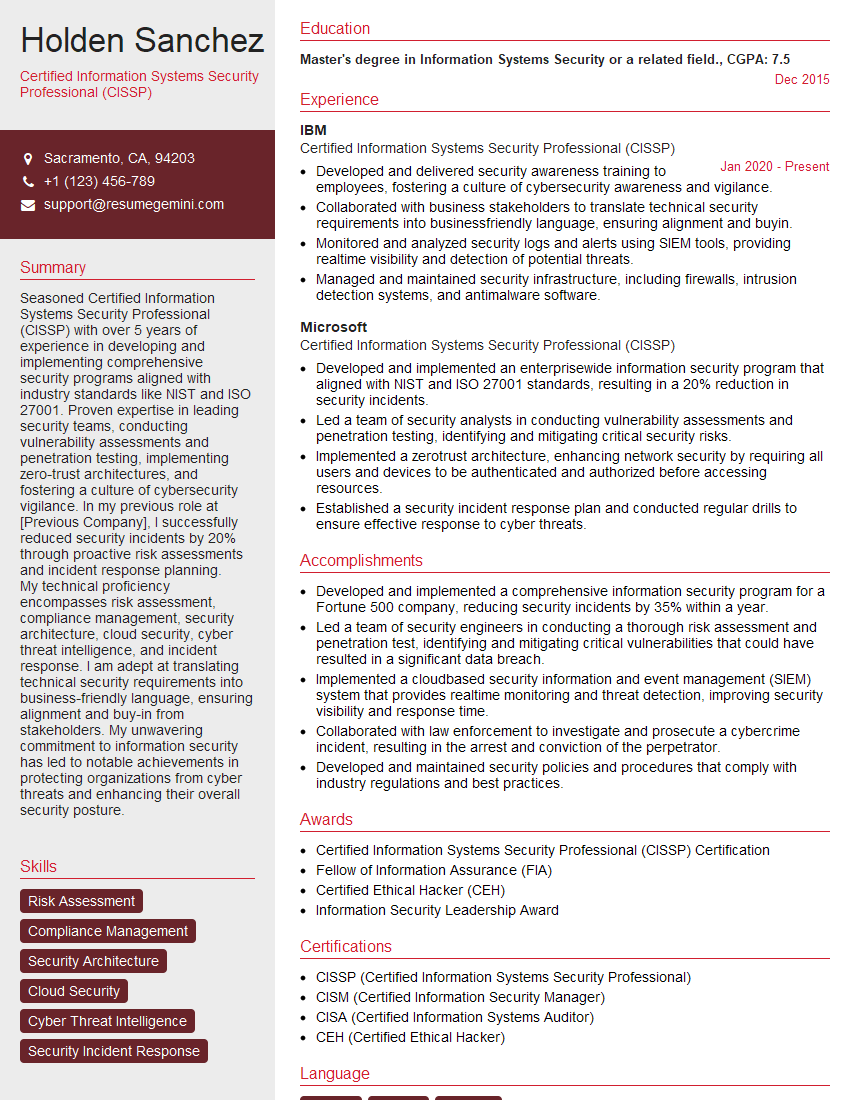
Acing the interview is crucial, but landing one requires a compelling resume that gets you noticed. Crafting a professional document that highlights your skills and experience is the first step toward interview success. ResumeGemini can help you build a standout resume that gets you called in for that dream job.
Essential Interview Questions For Certified Information Systems Security Professional (CISSP)
1. Describe the CIA triad and how it relates to information security?
The CIA triad is a model that describes the three main goals of information security: confidentiality, integrity, and availability. Confidentiality refers to protecting information from unauthorized disclosure, integrity refers to protecting information from unauthorized modification, and availability refers to ensuring that information is accessible to authorized users when needed.
- Confidentiality: This ensures that only authorized individuals have access to sensitive information.
- Integrity: This ensures that information remains accurate and complete.
- Availability: This ensures that information is available when needed.
2. Explain the different types of security assessments and when each one should be used?
Vulnerability Assessment
- Identifies potential vulnerabilities in a system or network.
- Uses automated tools to scan for known vulnerabilities.
Penetration Testing
- Simulates real-world attacks to identify exploitable vulnerabilities.
- Requires skilled security professionals to conduct.
Risk Assessment
- Evaluates the likelihood and impact of potential threats.
- Helps organizations prioritize security measures.
3. Discuss the different methods of encryption and their strengths and weaknesses?
Encryption is the process of converting plaintext into ciphertext using an algorithm and a key. The ciphertext can only be decrypted using the same key or its counterpart. Different encryption methods include:
- Symmetric-Key Encryption: Uses a single key for both encryption and decryption. (e.g., AES, DES)
- Asymmetric-Key Encryption: Uses two different keys, a public key for encryption and a private key for decryption. (e.g., RSA, ECC)
- Hashing: Converts input data into a fixed-size output called a hash. Used for data integrity and digital signatures.
4. Describe the different types of network security controls and their purposes?
- Firewalls: Block unauthorized access to a network.
- Intrusion Detection Systems (IDS): Monitor network traffic for suspicious activity.
- Virtual Private Networks (VPNs): Create a secure tunnel for remote access.
- Access Control Lists (ACLs): Define who can access specific resources.
5. Explain the different types of security audits and their benefits?
- Compliance Audit: Verifies compliance with regulations and standards.
- Operational Audit: Assesses the effectiveness of security controls.
- Technical Audit: Reviews the security of technical systems and networks.
Benefits include:
- Improved security posture
- Compliance with regulations
- Identification of security weaknesses
6. Discuss the different types of security incident response plans and their components?
- Incident Response Plan: Outlines the steps to be taken in the event of a security incident.
- Incident Response Team: A team of individuals responsible for responding to security incidents.
- Incident Response Process: The process followed during an incident response, including containment, eradication, recovery, and reporting.
7. Explain the role of encryption in cloud computing?
Encryption plays a crucial role in cloud computing by protecting data at rest and in transit:
- Data at Rest: Encrypts data stored in cloud storage services to prevent unauthorized access.
- Data in Transit: Encrypts data transmitted between cloud services and client devices to protect against eavesdropping.
8. Describe the principles of least privilege and separation of duties in information security?
The principle of least privilege states that users should only have the minimum level of access necessary to perform their job functions. Separation of duties is the practice of assigning different tasks to different individuals to reduce the risk of fraud or errors.
- Least Privilege: Prevents unauthorized access to sensitive data and functionality.
- Separation of Duties: Minimizes the impact of a single individual’s compromise.
9. Explain the importance of security awareness and training for employees?
Security awareness and training programs educate employees about security risks and best practices. They help:
- Reduce the risk of human error
- Increase employee vigilance against phishing attacks
- Promote responsible behavior with sensitive information
10. Discuss the ethical considerations in information security?
- Confidentiality: Respecting the privacy of individuals.
- Integrity: Ensuring the accuracy and completeness of information.
- Availability: Balancing security measures with user accessibility needs.
- Accountability: Taking responsibility for security decisions and actions.
Interviewers often ask about specific skills and experiences. With ResumeGemini‘s customizable templates, you can tailor your resume to showcase the skills most relevant to the position, making a powerful first impression. Also check out Resume Template specially tailored for Certified Information Systems Security Professional (CISSP).
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Great Savings With New Year Deals and Discounts! In 2025, boost your job search and build your dream resume with ResumeGemini’s ATS optimized templates.
Researching the company and tailoring your answers is essential. Once you have a clear understanding of the Certified Information Systems Security Professional (CISSP)‘s requirements, you can use ResumeGemini to adjust your resume to perfectly match the job description.
Key Job Responsibilities
Certified Information Systems Security Professionals (CISSPs) are experts in protecting information systems from unauthorized access, use, disclosure, disruption, modification, or destruction. They play a critical role in safeguarding sensitive data and ensuring the integrity of information systems.
1. Risk Identification and Assessment
CISSPs assess risks to information systems to identify potential vulnerabilities that could be exploited by attackers and determine the likelihood and impact of these risks.
2. Security Policy Development and Implementation
They participate in developing and implementing security policies and procedures to protect the confidentiality, integrity, and availability of information systems.
3. Security Incident Response
CISSPs develop and implement incident response plans and procedures to be followed in the event of a security incident, and manage the incident response process to minimize damage.
4. Security Awareness and Training
They develop and deliver security awareness training and education programs to employees to raise awareness of security risks and promote good security practices.
Interview Tips
1. Research the Company and Position
Before the interview, learn about the organization, its industry, and its security needs. This will help you understand the context of the role and tailor your answers to the specific requirements.
2. Review the CISSP Common Body of Knowledge (CBK)
The CBK is the foundation of the CISSP certification and covers the eight domains of information security. Refamiliarize yourself with the CBK concepts to demonstrate a comprehensive understanding of the field.
3. Prepare Specific Examples
When answering interview questions, provide specific examples from your experience that demonstrate your skills and abilities in information security. Quantify your accomplishments whenever possible to provide tangible evidence of your impact.
4. Highlight Transferable Skills
If you don’t have direct experience in all areas of the CISSP CBK, emphasize transferable skills. Highlight experiences where you demonstrated analytical thinking, problem-solving, risk management, communication, and teamwork abilities.
5. Be Professional and Enthusiastic
Dress professionally, arrive on time, and maintain a positive and enthusiastic demeanor. Engage with the interviewer, ask thoughtful questions, and convey your passion for information security.
Next Step:
Now that you’re armed with interview-winning answers and a deeper understanding of the Certified Information Systems Security Professional (CISSP) role, it’s time to take action! Does your resume accurately reflect your skills and experience for this position? If not, head over to ResumeGemini. Here, you’ll find all the tools and tips to craft a resume that gets noticed. Don’t let a weak resume hold you back from landing your dream job. Polish your resume, hit the “Build Your Resume” button, and watch your career take off! Remember, preparation is key, and ResumeGemini is your partner in interview success.