Are you gearing up for a career shift or aiming to ace your next interview? Look no further! We’ve curated a comprehensive guide to help you crack the interview for the coveted Cryptographic Vulnerability Analyst position. From understanding the key responsibilities to mastering the most commonly asked questions, this blog has you covered. So, buckle up and let’s embark on this journey together.
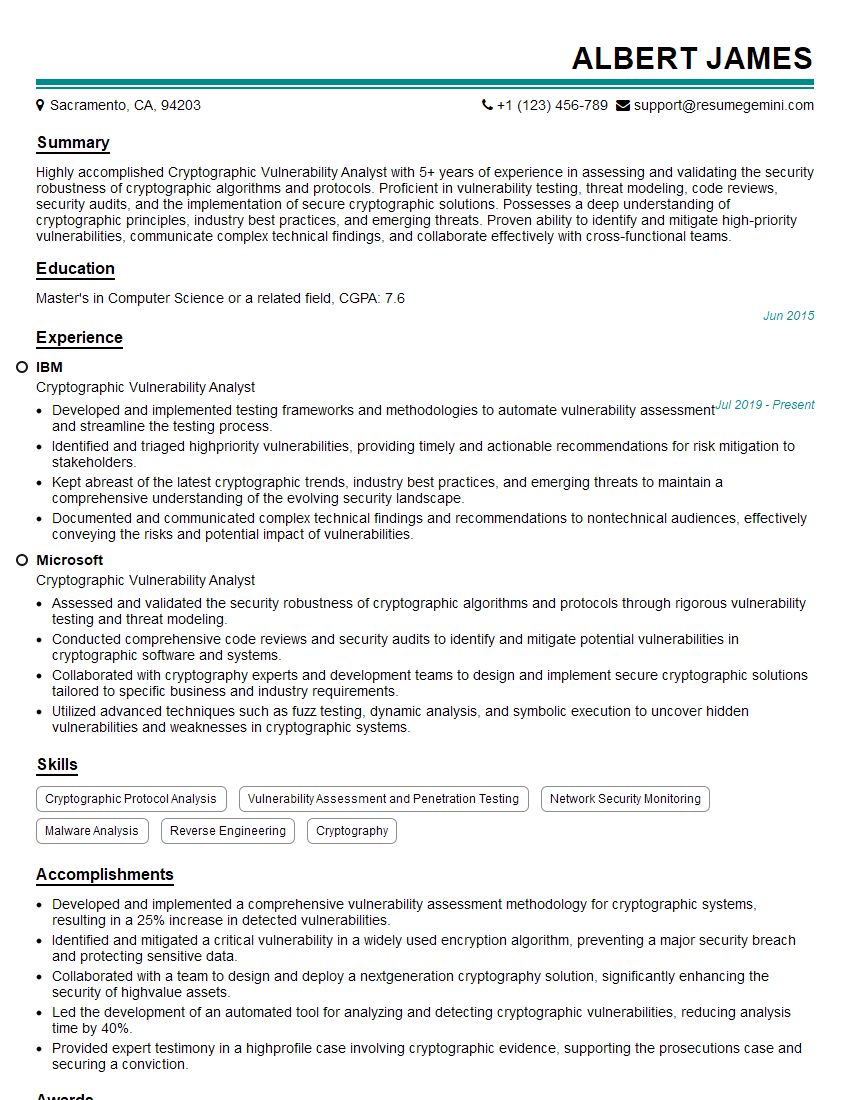
Acing the interview is crucial, but landing one requires a compelling resume that gets you noticed. Crafting a professional document that highlights your skills and experience is the first step toward interview success. ResumeGemini can help you build a standout resume that gets you called in for that dream job.
Essential Interview Questions For Cryptographic Vulnerability Analyst
1. Explain how public-key cryptography works and provide an example of how it can be used in real-world applications.
Public-key cryptography is a cryptographic system that uses two different keys: a public key and a private key. The public key is used to encrypt data, while the private key is used to decrypt data. This system is based on the mathematical problem of factoring large numbers. It is computationally infeasible to factor large numbers, which makes it difficult to break the encryption.
One real-world application of public-key cryptography is in the Secure Socket Layer (SSL) protocol. SSL is used to encrypt data transmitted over the Internet. When a user visits a website that uses SSL, their browser will establish a secure connection with the website. The browser will use the website’s public key to encrypt the data that is sent to the website. The website will then use its private key to decrypt the data.
2. Describe the different types of cryptographic attacks and how they can be mitigated.
Brute-force attacks
- In a brute-force attack, the attacker tries all possible combinations of characters to find the correct password or encryption key.
- This type of attack can be mitigated by using strong passwords or encryption keys.
Dictionary attacks
- In a dictionary attack, the attacker uses a list of common words or phrases to try to guess the password or encryption key.
- This type of attack can be mitigated by using passwords or encryption keys that are not common words or phrases.
Phishing attacks
- In a phishing attack, the attacker sends an email or text message that appears to be from a legitimate organization, such as a bank or a government agency.
- The email or text message will contain a link to a website that looks like the legitimate organization’s website, but is actually a fake website.
- The attacker will try to trick the user into entering their password or other personal information on the fake website.
- This type of attack can be mitigated by being aware of phishing scams and by not clicking on links in emails or text messages from unknown senders.
3. Explain the concept of key management and why it is important.
Key management is the process of generating, storing, and using cryptographic keys. It is important to manage keys properly to ensure that they are kept secure and that they are used correctly.
There are a number of different key management systems available. The best key management system for a particular organization will depend on the organization’s specific needs.
4. Describe the role of a cryptographic vulnerability analyst.
- A cryptographic vulnerability analyst is responsible for identifying and mitigating cryptographic vulnerabilities in software and systems.
- This involves analyzing cryptographic algorithms, protocols, and implementations to find vulnerabilities that could be exploited by attackers.
- Cryptographic vulnerability analysts also develop and implement countermeasures to protect against cryptographic attacks.
5. What are some of the common challenges faced by cryptographic vulnerability analysts?
- The complexity of cryptographic algorithms and protocols can make it difficult to identify vulnerabilities.
- The constantly evolving nature of the threat landscape means that cryptographic vulnerability analysts must constantly stay up-to-date on the latest threats.
- The lack of awareness of cryptography among software developers can lead to vulnerabilities being introduced into software.
6. What are some of the best practices for cryptographic vulnerability analysis?
- Use a systematic approach to vulnerability analysis.
- Use a variety of tools and techniques to identify vulnerabilities.
- Collaborate with other security professionals to share knowledge and expertise.
- Stay up-to-date on the latest threats and vulnerabilities.
7. How can I improve my skills as a cryptographic vulnerability analyst?
- Take courses on cryptography and vulnerability analysis.
- Read books and articles on cryptography and vulnerability analysis.
- Attend conferences and workshops on cryptography and vulnerability analysis.
- Practice identifying and mitigating cryptographic vulnerabilities.
8. What are some of the emerging trends in cryptographic vulnerability analysis?
- The use of machine learning and artificial intelligence to identify vulnerabilities.
- The development of new cryptographic algorithms and protocols.
- The increasing use of cryptography in cloud computing and other emerging technologies.
9. What are some of the challenges facing cryptographic vulnerability analysts in the future?
- The increasing complexity of cryptographic algorithms and protocols.
- The constantly evolving threat landscape.
- The lack of awareness of cryptography among software developers.
10. What are some of the opportunities for cryptographic vulnerability analysts in the future?
- The growing demand for cryptographic vulnerability analysts.
- The development of new tools and techniques for vulnerability analysis.
- The increasing use of cryptography in new technologies.
Interviewers often ask about specific skills and experiences. With ResumeGemini‘s customizable templates, you can tailor your resume to showcase the skills most relevant to the position, making a powerful first impression. Also check out Resume Template specially tailored for Cryptographic Vulnerability Analyst.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Great Savings With New Year Deals and Discounts! In 2025, boost your job search and build your dream resume with ResumeGemini’s ATS optimized templates.
Researching the company and tailoring your answers is essential. Once you have a clear understanding of the Cryptographic Vulnerability Analyst‘s requirements, you can use ResumeGemini to adjust your resume to perfectly match the job description.
Key Job Responsibilities
Cryptographic Vulnerability Analysts are responsible for identifying, analyzing, and mitigating vulnerabilities in cryptographic systems. They work with a variety of stakeholders, including software developers, security engineers, and business leaders, to ensure that cryptographic systems are secure and compliant with regulations.
Their responsibilities include:
1. Vulnerability Assessment and Analysis
Cryptographic Vulnerability Analysts conduct vulnerability assessments to identify weaknesses in cryptographic systems. They use a variety of techniques, such as code review, penetration testing, and fuzzing, to find vulnerabilities that could be exploited by attackers.
- Conduct vulnerability assessments to identify weaknesses in cryptographic systems
- Use a variety of techniques, such as code review, penetration testing, and fuzzing, to find vulnerabilities
2. Vulnerability Mitigation
Once a vulnerability has been identified, Cryptographic Vulnerability Analysts develop and implement mitigation strategies. This may involve patching software, updating configurations, or implementing new security controls. They also work with software developers to fix vulnerabilities in their code.
- Develop and implement mitigation strategies to address vulnerabilities
- Work with software developers to fix vulnerabilities in their code
3. Risk Assessment and Management
Cryptographic Vulnerability Analysts assess the risks associated with cryptographic vulnerabilities and develop strategies to manage those risks. They consider the likelihood of an attack, the potential impact of an attack, and the cost of mitigating the vulnerability.
- Assess the risks associated with cryptographic vulnerabilities
- Develop strategies to manage those risks
4. Compliance and Reporting
Cryptographic Vulnerability Analysts must comply with a variety of regulations, including the Payment Card Industry Data Security Standard (PCI DSS) and the Health Insurance Portability and Accountability Act (HIPAA). They also report on the security of cryptographic systems to management and stakeholders.
- Comply with a variety of regulations, including PCI DSS and HIPAA
- Report on the security of cryptographic systems to management and stakeholders
Interview Tips
Cryptographic Vulnerability Analyst, is a highly specialized role in the world of Information Security, there are few tips for acing an interview for this position.
1. Research the Company and the Role
Before your interview, take the time to research the company and the specific role you are applying for. This will help you understand the company’s security needs and the skills and experience that are required for the job.
- Visit the company’s website to learn about their business, their security posture, and their culture.
- Read the job description carefully and identify the key skills and experience that the company is looking for.
- Use LinkedIn to connect with current and former employees of the company to get insights into the company culture and the role.
2. Highlight Your Relevant Experience and Skills
In your interview, be sure to highlight your relevant experience and skills in cryptography and vulnerability assessment. You should also be able to clearly articulate your understanding of the risks associated with cryptographic vulnerabilities and your experience in mitigating those risks.
- Quantify your experience whenever possible. For example, instead of saying “I have experience in vulnerability assessment,” you could say “I have conducted over 100 vulnerability assessments and identified over 500 vulnerabilities.”.
- Be prepared to discuss your experience in a variety of cryptographic areas, such as encryption, hashing, and digital signatures.
- Be able to clearly articulate your understanding of the risks associated with cryptographic vulnerabilities.
3. Be Prepared to Answer Technical Questions
Interviewers will likely ask you a series of technical questions to assess your knowledge of cryptography and vulnerability assessment. Be prepared to answer questions about topics such as:
- Encryption algorithms
- Hashing functions
- Digital signatures
- Vulnerability assessment techniques
- Risk assessment and management
- Compliance with regulations
4. Be Professional and Enthusiastic
First impressions matter, so be sure to dress professionally and arrive on time for your interview. Also, be enthusiastic about the role and the company. This will show the interviewer that you are genuinely interested in the position and that you would be a valuable asset to the team.
- Dress professionally and arrive on time for your interview.
- Make eye contact with the interviewer and speak clearly and confidently.
- Be enthusiastic about the role and the company.
- Ask thoughtful questions at the end of the interview.
Next Step:
Now that you’re armed with interview-winning answers and a deeper understanding of the Cryptographic Vulnerability Analyst role, it’s time to take action! Does your resume accurately reflect your skills and experience for this position? If not, head over to ResumeGemini. Here, you’ll find all the tools and tips to craft a resume that gets noticed. Don’t let a weak resume hold you back from landing your dream job. Polish your resume, hit the “Build Your Resume” button, and watch your career take off! Remember, preparation is key, and ResumeGemini is your partner in interview success.